How to protect CVE-2021-44228 / Log4Shell using Innoculator
Currently at Innoculator, the team are deep in testing our platform before making it generally available to the public (Not long now…). But whilst we are doing this, I thought I would share how easy (and groundbreaking) Innoculator makes it to virtually patch something as common as Log4Shell. I know we talk about this vulnerability […]
The importance of Lateral Movement in Defence Plans

In the ever-evolving landscape of cybersecurity, lateral movement remains one of the most underestimated tactics utilised by attackers. While organizations often focus on securing their perimeters, the internal pathways that attackers exploit to move laterally within networks are frequently forgotten. This oversight can have devastating consequences, as lateral movement is a critical phase in an […]
2024 –The curious case of the 10.0 CVSS score

As we look back at the cybersecurity landscape over the past few years, it is clear that 2024 stands out as a remarkable year in terms of the sheer volume of critical vulnerabilities discovered. However, one thing sticks out like a sore thumb. The number of CVEs (Common Vulnerabilities and Exposures) with a perfect CVSS […]
Innoculator version 1.0 released

What happens when you combine AI with virtual patching? You solve the vulnerability and legacy software problem. Melbourne, Australia – After a year of dedicated development, we are thrilled to announce the release of Innoculator, an AI-powered application protection platform. Innoculator is designed to provide virtual patches for any known vulnerability, including those in legacy […]
Legacy Software Breaches- A couple of lessons from history
As we here at Innoculator excitedly get ready for our product launch, we thought we would dive a bit deeper into a couple of pertinent case studies that helped us realise the extent of the dangers and problems inherent in securing your Legacy Software. These systems are usually (otherwise why would you keep them?) integral […]
We STILL need to talk about Log4j

We started this blog at the start of last year with a post titled “We need to talk about Log4J”. With the year coming to an end and 2025 kicking off, we thought we should look at how that particular CVE has been progressed during the past year. To recap, three years ago the cybersecurity […]
Is Vulnerability Management Broken?
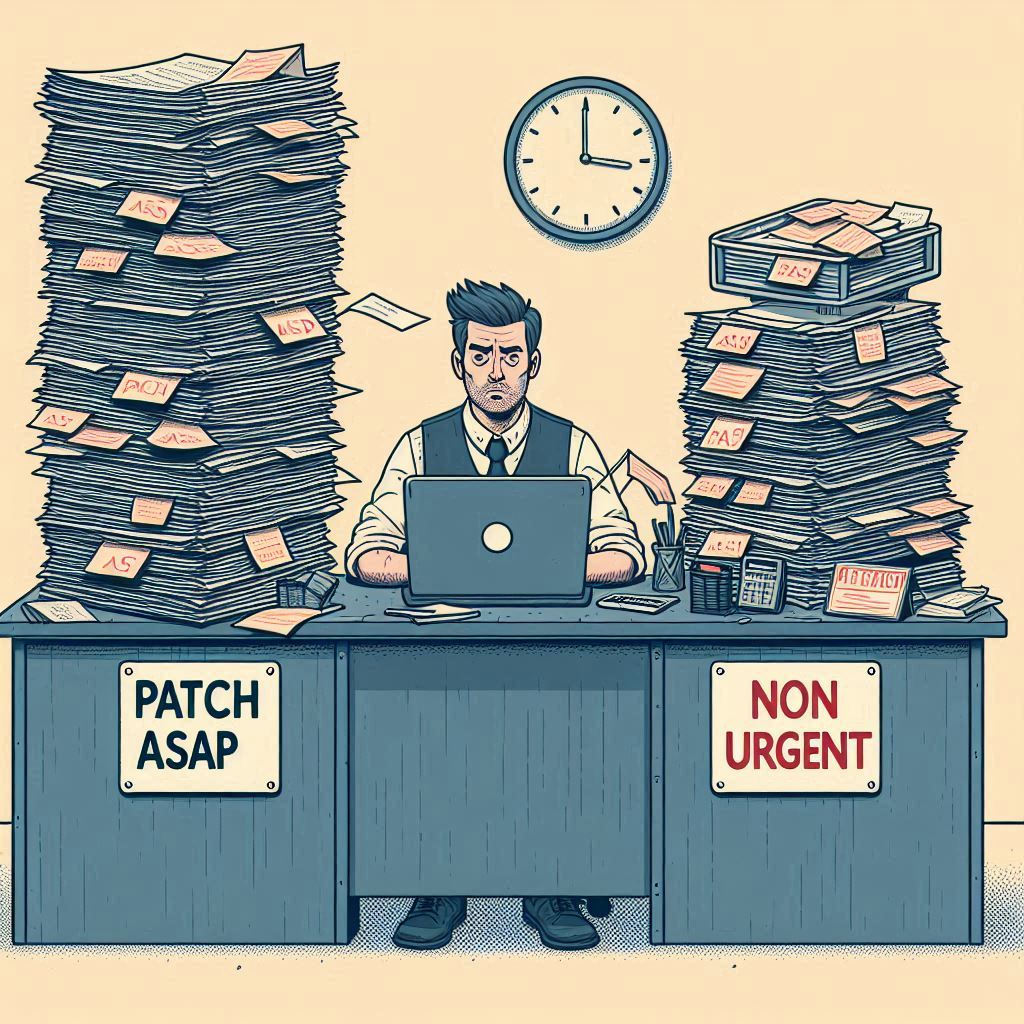
In today’s IT landscape, organizations face a relentless range of cyber threats. To counter these, vulnerability management has become a cornerstone of good cybersecurity management. However, despite significant investments in tools and personnel, many businesses still struggle to protect their systems effectively, with countless examples of unpatched systems becoming a key stepping stone in any […]
The Illusion of Security: How Rules of Engagement Can Mislead
In the realm of cybersecurity pen-testing, the Rules of Engagement (ROE) are pivotal for structured, ethical hacking and vulnerability assessments. They specify what can and cannot be done during a red team engagement, ensuring that the testing is both controlled and ethical. However, while these rules are essential, they can sometimes foster a false sense […]
The Conundrum of Legacy Applications

Legacy applications are software systems that have been in use for a long time and are based on outdated/ unpatched software. Despite their age, these applications continue to be critical to the operations of many organizations. They often run on older hardware and may not be compatible with modern systems or software. The term “legacy” […]
Recent Events & the Patch Gap

Let me be clear this isn’t a blog about apportioning blame to anyone. These sort of events have happened multiple times in the past, perhaps not on the same scale, but this certainly isn’t the first nor will it be the last time an update from a supplier causes production issues. As we are all […]
